HBluetooth Security seems to be very good compared to 802.11 problems. But most of the Bluetooth Security is based the PIN you have to enter during pairing two devices or on the link key, which is a result of it. In addition Bluetooth uses much more channels and hops frequently within the spectrum, which makes Analyzing a real pain. Sniffing raw communication without being paired is until now only available to rich companies or individuals which could buy one of the over-priced Bluetooth Sniffers.
When i say High-Priced i talk about 10'000 US$. Frontline (http://www.fte.com) is one of the few Bluetooth Sniffer manufacturers and they sell their application together with a "special" Bluetooth sniffer ComProbe / dongle. Here are some marketing highlights from their FTS4BT product website:
Supports EDR (Enhanced Data Rate): FTS4BT is the only analyzer currently on the market to support Bluetooth v2.0 + EDR. - Finger-sized Bluetooth ComProbe: Air sniffing hardware is incredibly portable and requires no power. - Synchronized air and HCI sniffing: FTS4BT provides multiple points of observation, speeding up debug time. - Real-time debugging: FTS4BT captures, decodes, filters and displays data, and detects protocol errors simultaneously, all live and in real-time.
Decodes all Bluetooth protocols and most profiles. Quick release of new profiles to keep pace with changing Bluetooth specifications. - Extract Audio into WAV files for playback and analysis. - Includes Framedecoder for rapid development and seamless integration of HCI Vendor Extensions and other custom protocol implementations. - This Frontline technology is how we meet Bluetooth challenges.
Current: -------- It is in fact very easy to modify a very cheap standard USB dongle to be usable as comprobe and together with the nifty keygenerator, everyone can analyze Bluetooth. Follow the instructions below to get your Bluetooth raw sniffer for a few bugs. So for the marketing: This piece of reversing is how we meet the Frontline challenges :-) Warning: -------- Using a keygenerator to run illegal software copies is prohibited in many countries and you do it at your own risk. And we still think that you should buy this expensive tools if you do business with it. Prepare yourself: ----------------- To conduct all the steps you need the following: - Linux installation with Bluez and the important BCCMD, BDADDR and DFUTOOL from the CVS tree. Get it at http://www.bluez.org. A few security testing focused Linux distributions have them already pre-installed. - A supported CSR chip based Bluetooth dongle - A copy of the FTS4BT software (Should be available in combination with this howto) - A copy of the license and authentication code generator (Should be available in combination with this howto)
Step 1 - Backup original firmware: ---------------------------------- First you want to backup your USB sticks current firmware and configuration for later use. Follow the points below to do this: - Insert your stick into your linux machine and do a hciconfigup (Most often is hci0). Check using hciconfig -a if the device is there and UP. Looks somewhat similar to that list below i suggest that you copy your information to a safe place, in case you want to switch back to it: linux ~ # hciconfig -a hci0: Type: USB BD Address: 00:DE:EA:DB:EE:EF ACL MTU: 192:8 SCO MTU: 64:8 UP RUNNING RX bytes:85 acl:0 sco:0 events:9 errors:0 TX bytes:30 acl:0 sco:0 commands:8 errors:0 Features: 0xff 0xff 0x0f 0x00 0x00 0x00 0x00 0x00 Packet type: DM1 DM3 DM5 DH1 DH3 DH5 HV1 HV2 HV3 Link policy: Link mode: SLAVE ACCEPT Name: 'COMPUTER' Class: 0x000000 Service Classes: Unspecified Device Class: Miscellaneous, HCI Ver: 1.1 (0x1) HCI Rev: 0x33c LMP Ver: 1.1 (0x1) LMP Subver: 0x33c Manufacturer: Cambridge Silicon Radio (10)
- Write down your btaddr (similar to mac addr),in our case its 00:DE:EA:DB:EE:EF You will need it later on, so write it down. Tip: You can also set a specific address using the tool btaddr which als also from bluez. - Now just backup the current firmware using the dfutool. Please notice that ID 0a12:0001 thats the vendor and product id (You can also get it using lsub). We need the product to be 0002 but we do this a bit later. Now do your backup, it should look like the example below. Please not that doing this in virtual machines may fail.In addition you need to use again hciconfigup after the dfutool because it resets the state of the device.: linux ~ # dfutool -d hci0 archive my_bluetooth_dongle_firmware_backup.dfu Available devices with DFU support:
2) Bus 1 Device 2: ID 0a12:0001 Interface 2
Select device (abort with 0): 2
Firmware upload ... 358832 bytes
linux ~ # hciconfig hci0 up
Step 1 - View original configuration: ------------------------------------- Acording to the CSR specifications there are multiple places to read stuff on the stick. Depending on your product these can be different. In generel these are "Default" (0x0000), "param" (0x0008), "psi" (0x0001), "psf" (0x0002) and "psrom" (0x0004). You can use those values usind bccmd pslist -s. Its even more easy if you like to get a complete list of parameters, just use: linux ~ # bccmd -d hci0 pslist -s 0x000F >> backup-configuration look in there for the lines that contains something similar to these: "0x02bf - USB product identifier (2 bytes)" "0x02be - USB vendor identifier (2 bytes)" Now get the values of those two bytes: Use the following command to get the location of the product id: linux ~ # bccmd -d hci0 psget -s 0x000f 0x02bf USB product identifier: 0x0001 (1):
This is what we want to change later
linux ~ # bccmd -d hci0 psget -s 0x000f 0x02be
USB vendor identifier: 0x0a12 (2578):
If you have something different we have to change it as well
Step 2 - Change product ID: ---------------------------------------- Acording to the CSR specifications there are multiple places to store stuff. On most dongles we know about it the product id is stored in "psf" (0x0002). Never mind if its not there just check your configuration and search for it. If you the right location then use the following or similar line to modify the product id from 0x0001 to 0x0002. Otherwise Frontline drivers wont install properly. linux ~ # bccmd -d hci0 psset -s 0x0002 0x02bf 0x0002 new id If you got no feedback then it was successful, check it by reading that value again using: linux ~ # bccmd -d hci0 psget -s 0x000f 0x02bf USB product identifier: 0x0002 (2)
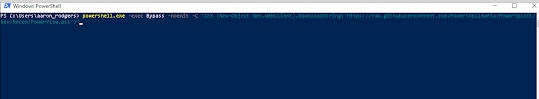
yeah data-blogger-escaped-baby="" data-blogger-escaped-pre="">Step 2 1/2 - Change vendor ID: ---------------------------------------- Most dongles i did see where Cambridged Silicon Radio,so its likely that you will get 0x0a12 as the usb vendor id. If you got that one, your finished with modifications on your dongle. Go to Step 3 of this guide. When you are using the Toshiba Version 2.0 + ERD dongle (which is amazing) you need to change also the vendor id from 0x0903 to 0x0a12 uing psget/psset. Step 3 - Install the sniffer software ------------------------------------- I guess i dont have to explain that. Use your license or generate one if you got a keygen :-). Please note, its important on the keygen that you enter the mac / btaddr of your dongle in lowercase and without any ":". The keygen is available as a linux binary as well as windows .exe file Use the serial number during installation. You will get a Desktop Folder with a lot of links. Don't delete it you will need it. Step 4 - Install the USB stick driver from frontline ---------------------------------------------------- When you insert your stick, windows will try to install a driver. You will find it in your Frontline installation dirctory, quite simple uh? Step 6 - Install the firmware package from frontline ---------------------------------------------------- Pretty straigth forward, but you will need it. Step 7 - Configure the sticks firmware etc. ------------------------------------------- Open the Bluetooth ComProbe Maintenance Utility. You find a shortcut on "Desktop\5.6.9.0 FTS4BT\Setup" or at similar places. Use the "Select Device" button and if you did previous steps correct, it will be detected. Yeah! Now use "Update Firmware" to update your desired firmware version (You will find it in the subfolder "Bluetooth ComProbe Firmware" in the frontline installation directory. I normaly use the latest one. After that you should use "Check Configuration" to configure the stick with the serial and the authentication code. Finally i suggest to use "Calibrate" which takes time. Step 8 - Use it --------------- Thats it. Future / Todo: ------- We did the first step and show you how to do it for less, now its the communities opurtunity to take that know-how and generate a custom, free firmware and sniffer module to generate a real opensource sniffer.